- This article was first published in LinkedIn on November 10, 2015 https://www.linkedin.com/pulse/how-secure-our-digital-identity-roberto-capodieci/
The use of digital signatures is becoming more and more popular. We digitally sign company share transfers, public records, contracts, emails (PGP), and many other legally valid electronic documents. For those of you that use cryptocurrencies (paying with bitcoins an online purchase), every transaction done in the blockchain is digitally signed.
A Digital Signature is unique to the person signing. This is why our digital identity is directly connected to our digital signature. Our “Public Key”, the unique identifier that is connected to our person, acts as an Identity Card number that institutions (such as banks or government entities) connect to our person through their KYC procedure. Once they see something signed by us, they have the legal right to claim that we did sign that.
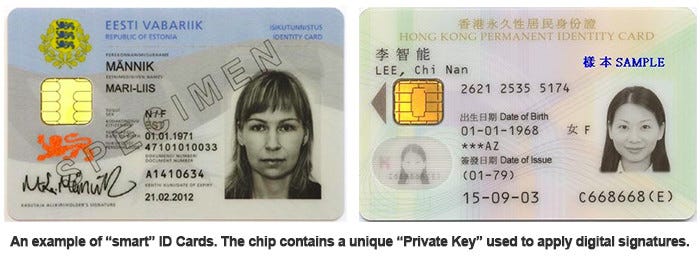
Each “Public Key” is accompanied by a “Private Key” that we must keep very safe, as it is the “secret data” used to digitally sign. We don’t even see it. It is a very long number embedded in the chip of a card, for example. Existing secure system are not very portable: are made of chipped cards, card readers, USB devices, and other very proprietary solution dependent on specific hardware devices. To overcome this gap, as the demand of digital signature is increasing incredibly, more and more mobile apps, or web solutions, have taken over the old secure systems. Now we store our “Secret Key” and digitally sign with and from our smartphones and notebooks. With the same devices we surf the web, we use applications, and we are exposed to spyware.

With banks embracing the blockchain technology, digital signature will be more and more a common occurrence, and such vulnerability (how the “private key” is stored) needs to be solved urgently.
As explained earlier, the private (or secret) key is a sort of password that is used to digitally sign transactions that, in this case, are then entered onto the blockchain. If a private key gets stolen, the thief can sign on behalf of the original owner and post irreversible transactions in his own favour.
No matter how securely you store your private key on your computer or smartphone, it always has to be exposed in the device’s memory when it’s used (to digitally sign something). That’s the inherent vulnerability and it just takes a virus with some malware or spyware to sniff the memory at the right moment, and the damage is done.
I been thinking to this problem since I been a victim myself one and a half year ago. I been studying this problem bottom up, searched for existing solutions, until I decided to do something about it by myself. This is where The Sound Key comes in. It is a device, very similar to banks’ OTP devices, to store your private key outside your computer or smartphone’s memory, and to digitally sign documents or blockchain transactions offline and therefore safely.

How the Sound Key works:
- The Sound Key connects to computers or cellphones through the headset port.
- The transaction data, as yet unsigned, are sent to the Sound Key via the audio port on your computer or smartphone.
- Having verified that the unsigned data in the Sound Key display is correct, type your password in the device to safely digitally sign the transaction.
- That’s it. Your transaction is signed, sealed, and ready to be delivered.
- The Sound Key will then transmit the signature back to your device through the audio or speaker port.
- At no stage does your secret key ever leave its safe place inside the Sound Key.

The Sound Key is currently a prototype, and I want to bring you the best of what it can do. I am therefore working not only on the device itself, but, we the help of experts, also on the accompanying software development kit, to be backed by good customer support, so that innovators and users alike can benefit from it as much as possible.
It’s anticipated that within a few years this kind of device will become widespread and popularly regarded as a necessity.
This is what happen when someone access your bitcoin private key: https://bitcoinmagazine.com/articles/bitcoin-researcher-has-bitcoins-stolen-from-private-key-on-shirt-1447447198

